Chinese Malware Hits Systems on Guam. Is Taiwan the Real Target?

Around the time the FBI was examining equipment obtained from a Chinese spy balloon that was shot down off the coast of South Carolina in February, US intelligence agencies and Microsoft discovered what they feared. was a more disturbing intruder: mysterious computer code that appeared in the telecommunications system in Guam. and elsewhere in the United States.
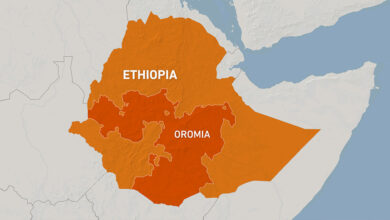
The code, which Microsoft claims was installed by a group of Chinese government hackers, has raised alarm bells because Guam, with its Pacific ports and vast US airbase, would be at the center of any US military response to an invasion or blockade of Taiwan. The operation is conducted with high stealth, sometimes running through home routers and other common consumer devices with internet connections, to make intrusions harder to track.
This code is known as a “web shell”, in this case a malicious script that allows remote access to the server. Home routers are especially vulnerable, especially older models that don’t yet have up-to-date software and protections.
not like hot air balloon fascinates Americans When it does piracy over sensitive nuclear sites, the computer code cannot be shot down on live television. So instead, Microsoft on Wednesday Publish details of the code that will make it possible for business users, manufacturers and others to detect and remove it. In a coordinated release, the National Security Agency — along with other domestic agencies and partners in Australia, the United Kingdom, New Zealand and Canada — publish a 24-page consultation referred to Microsoft’s findings and issued broader warnings about a “recently detected group of activity” from China.
Microsoft calls the hacker group “Hurricane Volt” and says it’s part of a Chinese state-sponsored effort to target not only critical infrastructure such as communications, electricity and gas utilities, but also maritime and transport operations. For now, the intrusions appear to be an espionage campaign. But the Chinese can use the code, designed to penetrate firewalls, to trigger destructive attacks, if they so desire.
So far, Microsoft said, there is no evidence that the Chinese group used access for any attacks. Unlike Russian groups, Chinese military and intelligence hackers often prioritize espionage.
In interviews, administration officials said they believe the code is part of China’s vast intelligence-gathering efforts covering cyberspace, outer space and, like humans, The US discovered with the hot air balloon incident, the lower atmosphere.
The Biden administration declined to discuss what the FBI found when they examined equipment recovered from the balloon. But the plane – more properly described as a giant flying vehicle – appears to include specialized radars and communications interceptors that the FBI has been examining since the balloon was shot down.
It is unclear whether the government’s silence about their findings from the balloon was motivated by a desire to prevent the Chinese government from knowing what the US had learned or to get over the diplomatic breach following the intrusion. .
On Sunday, speaking at a press conference in Hiroshima, Japan, President Biden addressed how the hot air balloon incident crippled already cold exchanges between Washington and Beijing. .
“And then this silly hot air balloon carrying spy gear worth as much as two cargo vans was flying over the United States, and it was shot down, and everything changed,” he told reporters. change the way they talk to each other”.
He predicts that relationships will “start to thaw very quickly.”
China has never admitted to infiltrating US networks, even in its biggest example: stealing the security check records of some 22 million Americans — including six million sets of fingerprints — from the Office of the Chinese Communists. Office of Human Resources Management during the Obama administration. That data theft lasted more than a year and led to an agreement between President Barack Obama and President Xi Jinping that led to a rapid decline in China’s malicious cyber activity.
On Wednesday, China sent out a warning to its companies to be on the lookout for American hacking. And there’s a lot of it too: In documents released by Edward Snowden, a former NSA contractor, there is evidence of US efforts to hack into the systems of Huawei, the Chinese telecommunications giant. States, as well as military and leadership goals.
Telecommunications networks are a prime target for hackers, and systems in Guam are especially important to China because military communications are often based on commercial networks.
Tom Burt, executive director of Microsoft’s threat intelligence unit, said in an interview that the company’s analysts – many of them veterans of the National Security Agency and other intelligence agencies – found the code “while investigating intrusion activity affecting a US port.” When they traced the breach, they found other networks were also attacked, “including some in the telecommunications sector in Guam.”
Anne Neuberger, deputy national security adviser for cyber and emerging technologies, says that covert efforts “like the activity exposed today are part of what drives us to focus on this.” telecommunications network security and the urgency to use “reliable providers” whose equipment meets established requirements. network security standards.
Ms. Neuberger has spearheaded the federal government’s effort to enforce new cybersecurity standards for critical infrastructure. Officials were surprised at the level of vulnerability in that infrastructure when one Russian ransomware attack on Colonial Pipeline in 2021 disrupted the flow of gasoline, diesel and jet fuel on the East Coast. After the attack, the Biden administration used the little-known powers of the Transportation Security Administration — the agency that regulates pipelines — to force private-sector utilities to comply. under a variety of cybersecurity tasks.
Now, Ms. Neuberger is promoting what she calls “an unwavering focus on improving the cybersecurity of our pipelines, rail systems, water systems and other critical services, ” includes mandates on cybersecurity practices for these areas, and works more closely with companies with “unique visibility” into threats to such infrastructure.
Those companies include Microsoft, Google, Amazon, and many telecommunications companies that can see activity on domestic networks. Intelligence agencies, including the NSA, are prohibited by law from operating inside the United States. But the NSA is allowed to publish the warnings, as it did Wednesday, along with the FBI and the Department of Homeland Security’s Cybersecurity and Infrastructure Administration.
The agency’s report is part of a relatively new move by the US government to release such data quickly in hopes of igniting practices like those of the Chinese government. In previous years, the United States generally withheld such information — sometimes categorizing it — and only shared it with select companies or organizations. But that almost always ensures that hackers can stay far ahead of the government.
In this case, the focus on Guam has particularly drawn the attention of officials who are assessing China’s ability — and its readiness — to attack or strangle Taiwan. Mr. Xi has ordered the People’s Liberation Army to potentially occupy the island by 2027. But the director of the CIA, William J. Burns, noted before Congress that order “doesn’t mean that he has decided to take the island.” intends to launch an invasion.”
Of the dozens of U.S. desk exercises conducted in recent years to map out what such an attack might look like, one of China’s first anticipated moves would be cut off US communications and slow down US response. So the exercises envision attacks on satellites and ground communications, especially around US facilities where military assets will be mobilized.
Nowhere is greater than Guam, where Andersen Air Force Base will be the starting point for many of the Air Force’s missions to help defend the island, and a very important Naval port for American submarines.